Imagine a stranger has stolen your login credentials, and they’re shopping with your credit card, sending emails from your work account, or accessing your company’s documents and files.
This is the reality of account takeover (ATO). The numbers paint a sobering picture of how ATO has become one of today’s most urgent cybersecurity challenges.
The ATO threat that’s keeping security leaders awake at night
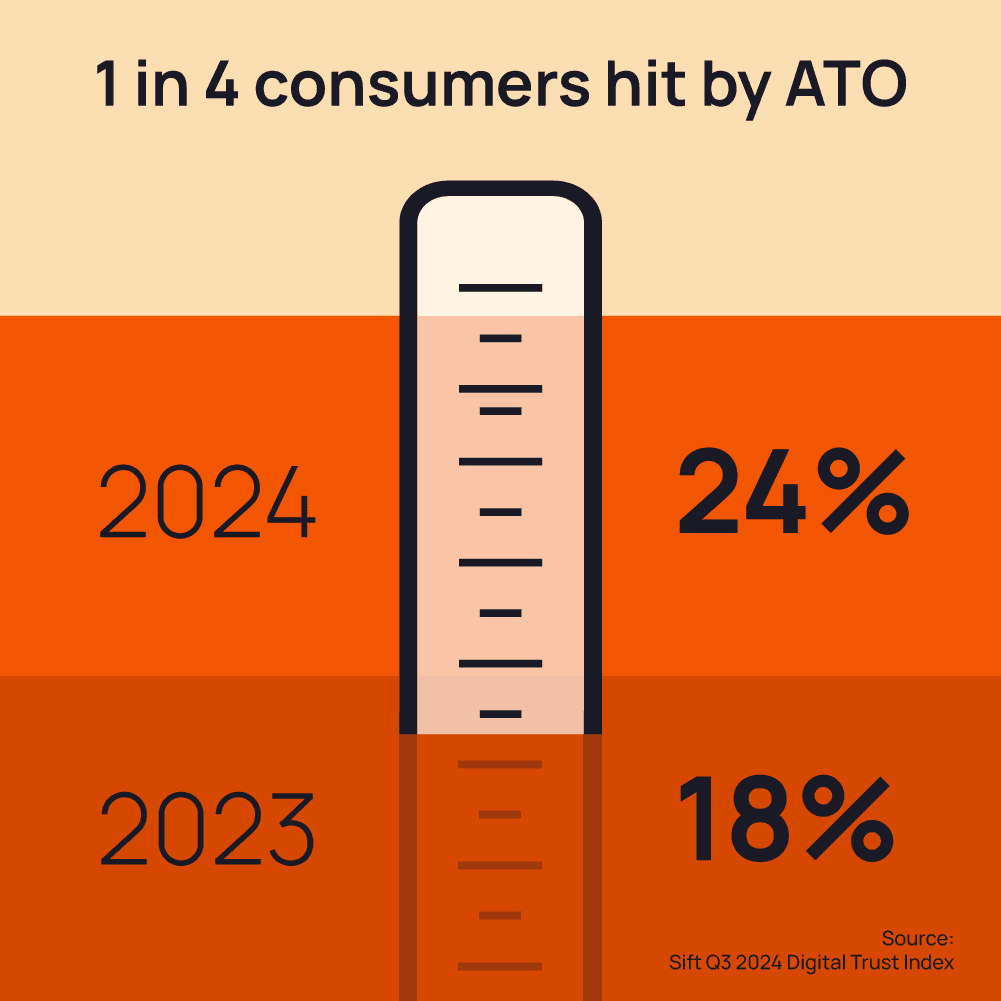
ATO attacks are devastatingly effective and alarmingly common. They increased by 24% between 2023 and 2024 (source: Sift). More than 67% of security professionals and leaders now consider ATO as one of their top four cyber threats (source: Abnormal 2024 State of Cloud Account Takeover Attacks report), along with ransomware, phishing, and denial of service attacks.
The financial cost of ATO attacks
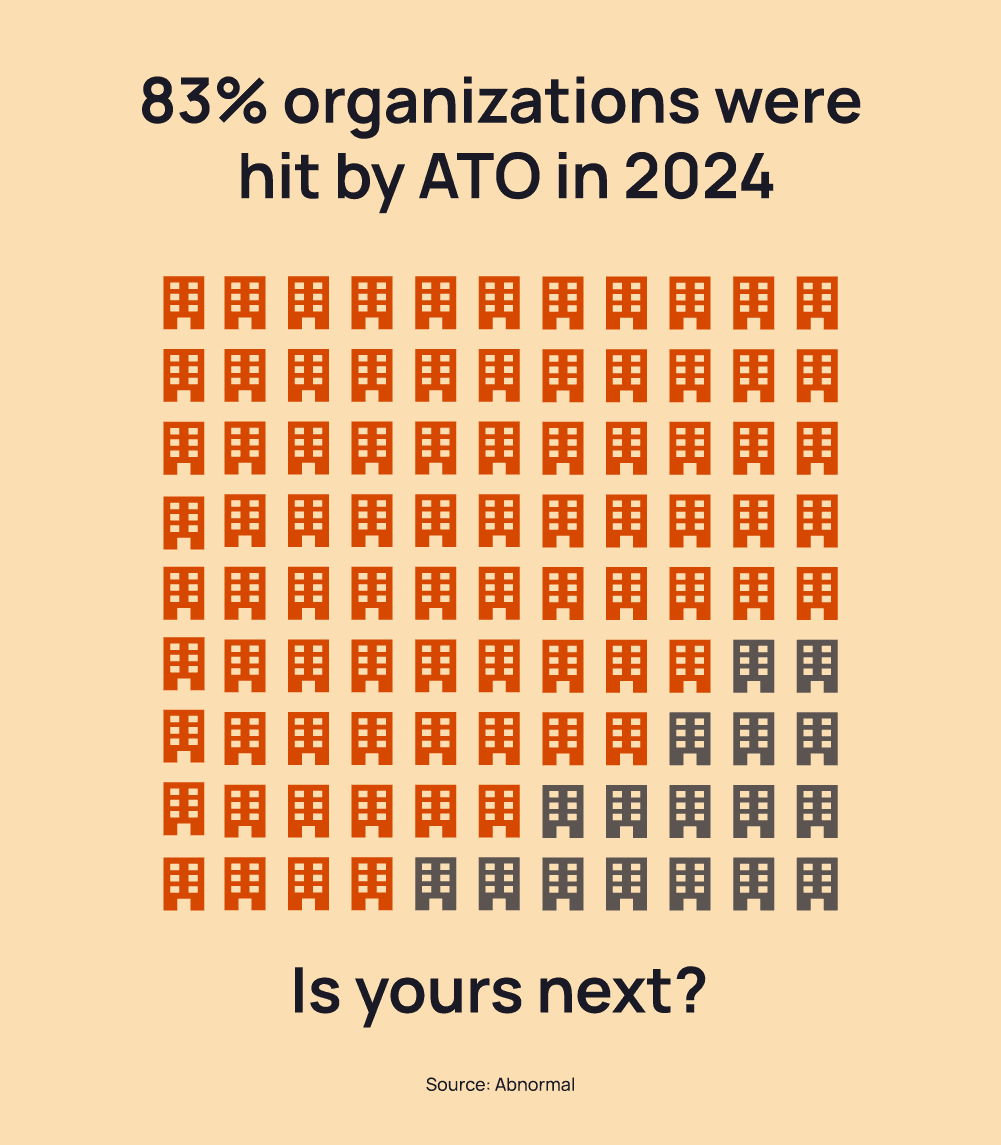
Account takeover fraud cost its victims around $15.6 billion in 2024 (source: 2025 AARP & Javelin Fraud Study). This was a 23% increase compared to 2023. What’s more, 83% of organizations experienced at least one ATO incident in 2024, and 45% experienced more than five (source: Abnormal).
The human cost of ATO attacks
Research has found that 24% of consumers fell victim to an ATO attack in 2024 (source: Sift Q3 2024 Digital Trust Index), an increase from 18% the previous year. That equates to one person in every four.
The effects extend beyond the immediate financial losses. Individual victims suffer the anxiety caused by a loss of privacy, plus the stress and hassle and recovering control of their accounts.
Organizations must deal with the cost and complexity of remediating the breach. They may also face regulatory punishments for failing to protect sensitive data. In the longer term, reputational damage can diminish their business. Four out of five consumers say they would stop buying from a site where they had been the victim of an ATO (source: Sift Q3 2024 Digital Trust Index). A single incident can wipe out customer trust that has taken years to build.
The silent victims
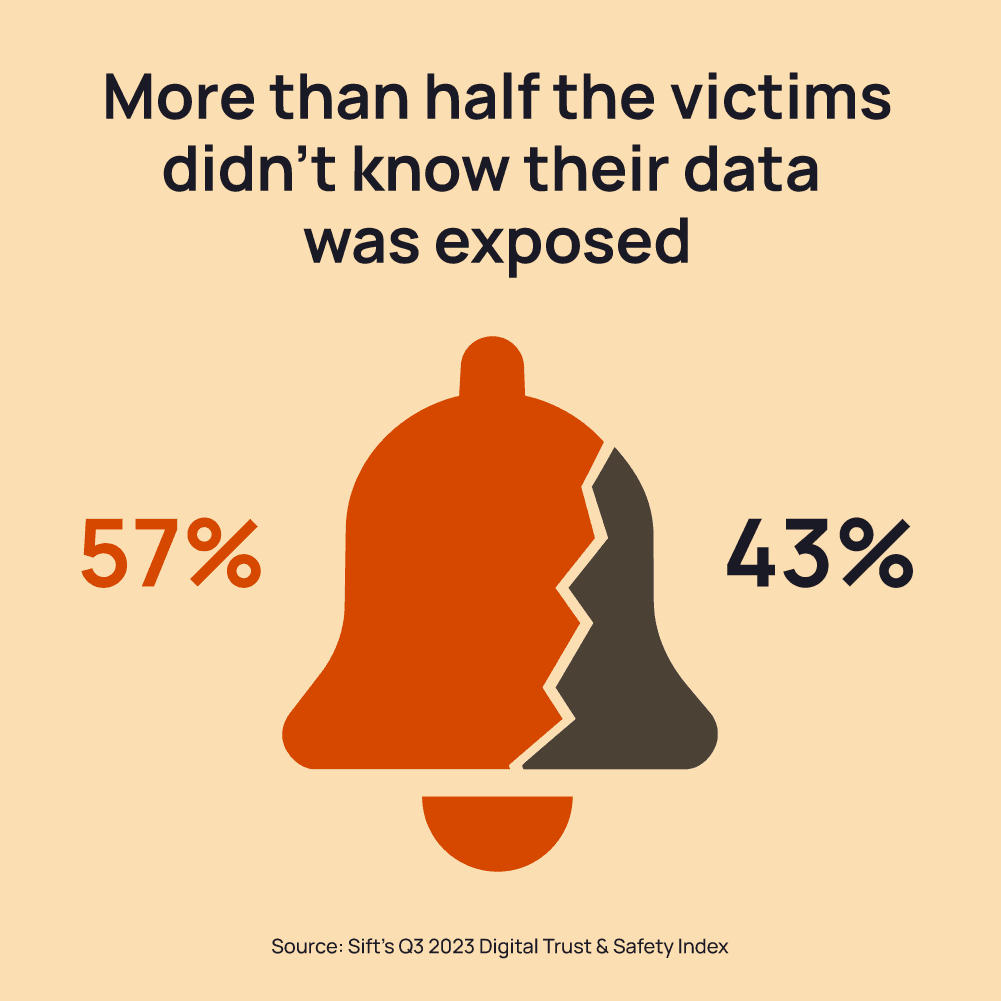
Only 43% of account takeover victims were notified by the company that their information had been compromised (source: Sift’s Q3 2023 Digital Trust & Safety Index). More than half of the victims remained in the dark, unaware that their digital identities had been hijacked. This is a critical failure.
When an account is taken over, it’s vital to act fast. Every minute that goes by leaves the attackers free to cause damage, pivot to other accounts, or sell stolen information in criminal forums and marketplaces.
How to defend your business against ATO attacks
ATO is now a cyber security crisis, and defenses aren’t keeping pace. To combat ATO, organizations need a multi-layered approach that combines employee education, authentication mechanisms, and proactive credential monitoring.
Educate your employees
Train everyone in your organization about phishing and credential theft. Make sure they understand the risks and know how to spot suspicious activity.
Strengthen authentication
Use multi-factor authentication (MFA) on all accounts and systems. Consider hardware security keys or biometric authentication for high-value accounts.
Implement strict password policies
Require strong, unique passwords. Credential monitoring also highlights risky behaviors, such as sharing passwords or reusing them across systems. That can help you to guide people towards best practices and strengthen your organization’s overall security.
Monitor for compromised credentials proactively
Credential monitoring solutions, such as Cybercheck, close this gap by detecting exposed passwords before attackers can exploit them. Cybercheck scans criminal forums and marketplaces for compromised credentials. If criminals are trading information about your organization, we alert you immediately. That means you can change your passwords and shut out potential attackers, before they use them to access your accounts and make you their next victim.







